Lox Game Studio Guides
Sections
Distributed Denial Of Service
Remote Access Trojan
How to Defend Yourself against DDoS And RAT
Lox-Guide#18012001140404041519 11/8/2018 - 12:52PM
In todays world, we all know that such attacks have increased in quantity and that if you are not protected well enough it will eventually result in your internet access to be interrupted.
What we will describe here are some simple instructions to help you gamers or home users to be protected without having to know how to program or having to use any softwares.
We tried to explain everything in the most short and understandable way possible, we hope that these informations will be useful for you.
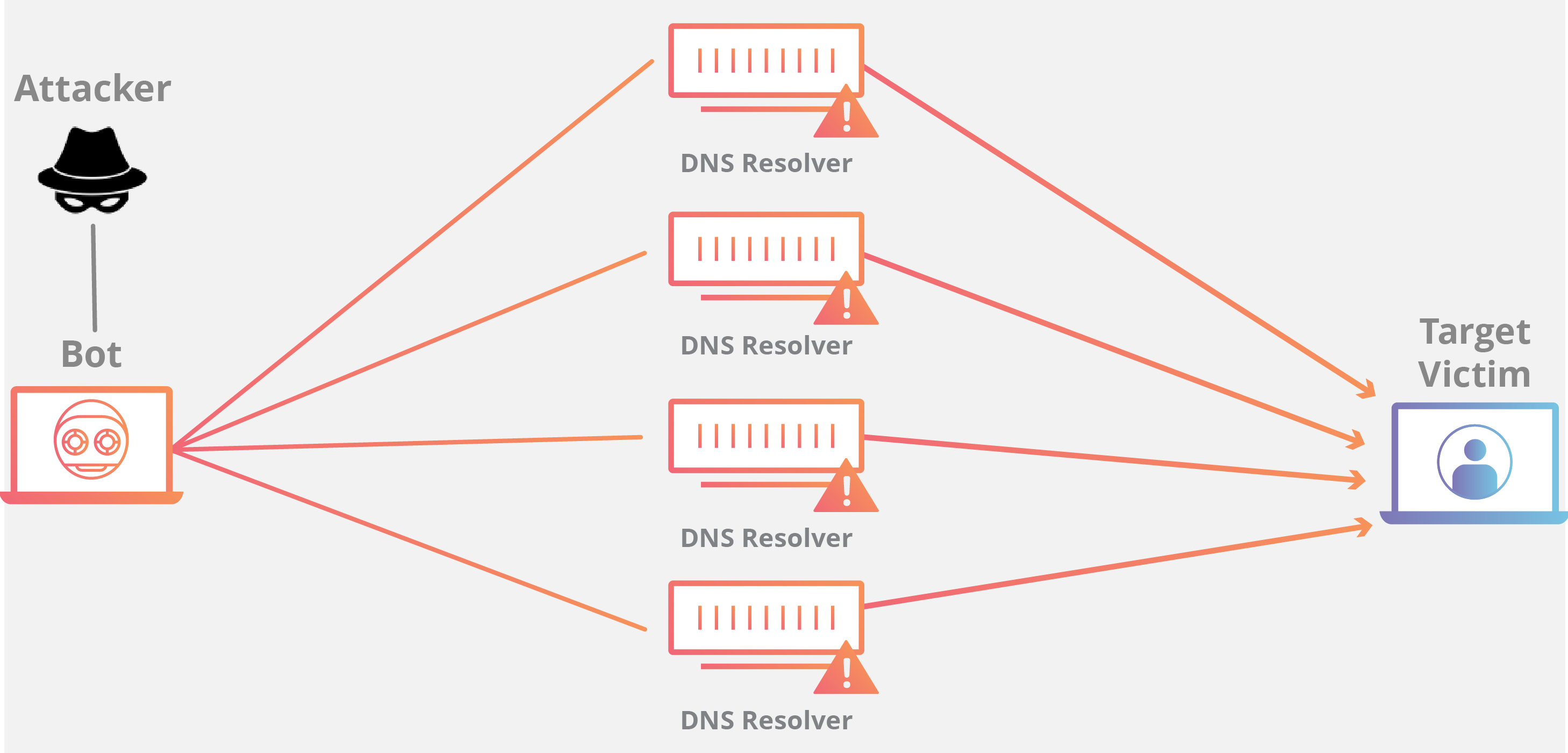
DDoS
DDoS (Distributed Denial of Service), is a cyber-attack type that aims to ensure that a machine or network resources cannot be accessed by the actual users by disrupting the services of the host that is connected to the internet, either indefinitely or temporarily.
Now we are going to show you the few steps to go through in case of being under a DDoS attack.
- Do not panic whatsoever, do not forget that a DDoS can only interrupt your connection to the internet, so it cannot harm anything else in any way.
- Try to find the software that is leaking your IP address, and shut it down.
- If you have a Dynamic IP: Turn off your router and wait for at least 10 seconds, then restart the router. This will result in your IP address to be changed.
- If you have a Static IP: Turn off your router and make a call to your internet provider letting them know that you are under a DDoS attack, depending on the service, approximately in 1 hour or so your internet provider will provide you with a new static IP address.
After these steps you can simply just restart (if using Dynamic IP) the router and continue your tasks.
However, if the insecure software is a community application such as Discord, Skype or Teamspeak, the thing you have to do is to find and learn what is causing the leak and prevent further problems. An attacker won't be able to get your IP address directly in Discord, but can find it from a Skype call. But if there is a vulnerability in the software itself, it can happen in any software, as long as you do not text or get into a call with the suspicious user, they should not be able to find out your IP address, however this might depend on how the software works.
Here are a few suggestions to help you protect your network from such attacks.
Using a Dynamic IP Address
A static IP won't change unless you ask for your provider to change it, making it harder for you to escape from cyber-attacks if your IP gets leaked, Dynamic IP addresses work differently from Static ones, they can be renewed by simply restarting your router, unplugging the network cable from your computer, or rejoining a Wi-Fi network, since whenever your router asks for an IP from your ISP when you rejoin a network it will be provided with a different one. So in case of a DDoS attack, all you have to do is finding and preventing the leak, and doing one of the above.
Use a VPN
A VPN won't let the attacker find your IP address. The VPN servers which are responsible with redirecting your network load, only shows the information and the IP address of the VPN server itself whenever a data gets sent to its destination, however don't forget that you shouldn't trust every VPN provider out there, because when you decide to agree with a VPN service they will be able to view all the data which aren't encrypted, and if there are any vulnerabilities in the VPN service you are using, in the case of them being attacked its possible for the attackers to get even into the encrypted data depending on the algorithm which they have been encrypted with. If you are looking for a VPN service which you will only use while surfing on the internet you can use the Opera browser which comes with a built-in free VPN service.
Since now we know that a DDoS attack can only interrupt your connection to the internet without being able to harm anything, let's get into a more dangerous type of a virus, called RAT (Remote Access Trojan)
What is a Remote Access Trojan?
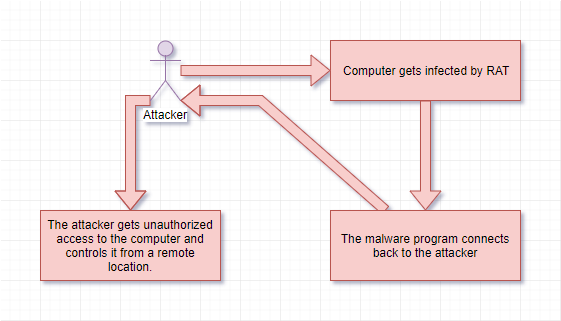
RAT, is a software type that the computer pirates use in order to get remote access of your computer, differently from Worm and other viruses, instead of aiming to harm your system it aims to leak data from it.
These type of attacks are generally used to steal the victims passwords and private informations, and mostly is not a threat for the general home users since its unlikely that they will be targeted.
If you think you are dealing with a RAT attack we highly suggest you to check your computer.
These steps will be only applicable for the Windows users.
- Start up your task manager and go into the network tab.
- Check the peformance/network tab and examine the data traffic (Send & Receive), if you have no applications open in the background and there is still a data transfer going on it can only mean that there is a problem.
- Investigate the Processes and Services tab, check if there are any unknown and suspicious services/programs are running, and after searching those services/programs in the internet, shut them down as long as they are not a part of the system.
- Go into your routers interface and close down or delete all of the ports if you have any open, its possible that they have found a way into your system through those open ports, and make sure you enable DMZ since it will prevent them from going into your routers interface and get your IP address.
We highly suggest you to use Eset Internet Security, not only will it find and delete viruses, Eset can detect attackers and prevent them from getting into your home network, if you're still not an Eset user, you can get a 30 days free trial by clicking here
If you're a standard computer user, or someone that loves to play games and surf in the internet in their free time without any knowledge about these subjects, you can always contact our Team since we will be glad to help you in any way we can.